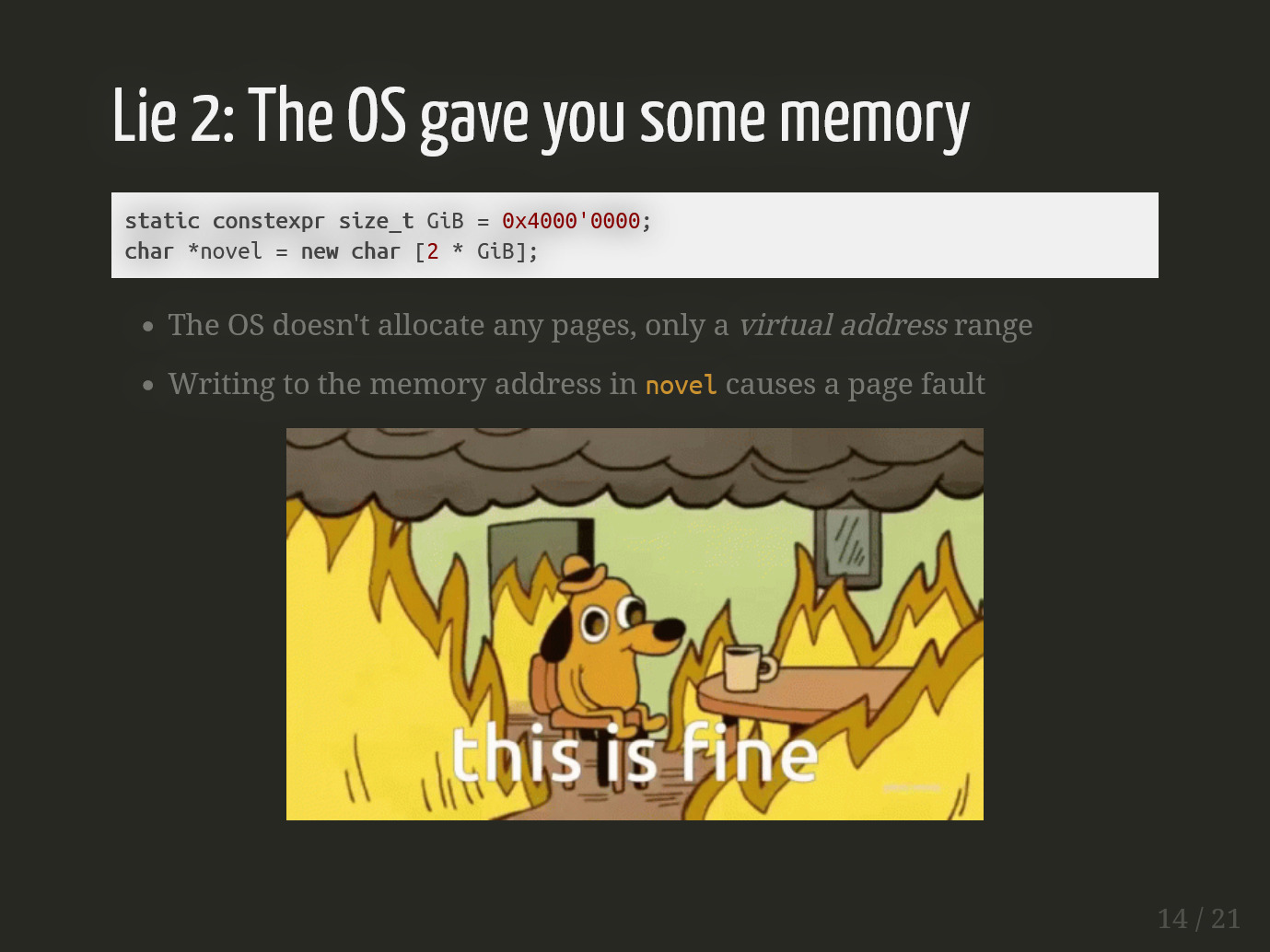
Lightning talk: Three lies your OS tells you about memory
At Echtra, we like to encourage folks to give small talks about topics in their areas of expertise. We have weekly C++ Fundamentals and Advanced C++, as well as monthly Lunch & Learn brown-bag sessions that don’t have to be as engineering-focused. It’s fun and it’s great for knowledge sharing and team growth. After finding out about my work on jsix, many of our engineers have often asked me to give talks on OS development and low-level programming.
Lightning talk: What happens before main()?
At Echtra, we like to encourage folks to give small talks about topics in their areas of expertise. We have weekly C++ Fundamentals and Advanced C++, as well as monthly Lunch & Learn brown-bag sessions that don’t have to be as engineering-focused. It’s fun and it’s great for knowledge sharing and team growth. After finding out about my work on jsix, many of our engineers have often asked me to give talks on OS development and low-level programming.
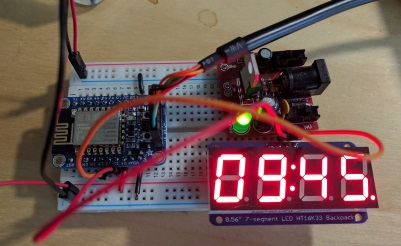
Meet the Pill-minder
Many of my projects are not born of necessity, but out of amusement or curiosity. Well, here’s one that does both. Without tools, I can be pretty forgetful, especially of mundane things. Fortunately, I’m pretty good at knowing this about myself and coming up with solutions. This is the first physical solution I’ve built, though.
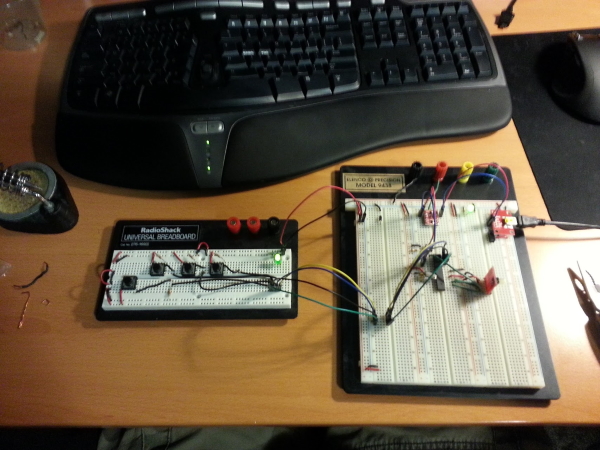
Building a Custom Chorded Keyboard
As some of you might know already, I like to nerd out about input devices. I’ve had the desire to build and try out a chorded keyboard ever since I first watched The Mother of all Demos. Chorded keyboards have had some popularity with wearable computing enthusiasts due to their one-handed use, but I thought they might also be interesting for ergonomic reasons. Building a chorded keyboard would also be a great learning experience as a deep dive into the workings of USB HID devices.

On Journey and Destiny
There’s a strange contradiction that I’ve been wrestling with for a little while. I thought that Journey was an absolutely beautiful and wonderful game. It even won eight awards at DICE this year, including “Game of the Year” and “Outstanding Achievement in Online Gameplay”. But here’s the thing: I think I might somehow be the only person in the world that really disliked Journey’s multiplayer system. If you haven’t played Journey, the multiplayer system works like this: you start playing the game as if you were playing a single-player game, and the game matches you with someone else who’s playing where you are.

GnuPG Dice!
Many months ago, I wrote a little GnuPG-verified dice CGI page for myself and my gaming group to use when resolving gaming situations over email. (Feel free to use it yourself, you can check it out here.) It’s inspired by other verified dice web applications out there. But while other scripts require you check a roll on the site itself, either by cut and pasting into a form, or by finding the roll in a list, I wanted something I could verify easily by looking at the message in my mail reader.

Symmetric NAT
I almost titled this post “Symmetric NAT considered harmful”, except I promised myself I’d never title something “considered harmful.” It seems like the number of consumer-level routers on the market that implement symmetric NAT (endpoint-dependent mapping) has been rising in recent years. This paper puts it as high as 16% in 2010 (with another 14% blocking UDP traffic, which, while tangential to this post, is really disappointing). RFC 4787 (Network Address Translation (NAT) Behavioral Requirements for Unicast UDP) is the “Best Common Practices” document regarding developing NAT devices and how they should behave.

Multi-processor compilation in older Visual Studios
I’m working from home today due to Seattle’s OMGSNOWPOCALYPSE2012. Lamenting the lack of IncrediBuild here at home, I decided to parallelize my builds - if only across four cores instead of across the entire office. Visual Studio 2010 has an option for parallelizing C++ builds within a single project (as opposed to parallelizing the building of multiple projects, which has long been supported) in the project configuration properties under C/C++ → General → Multi-processor Compilation.

Bandwidth Woes
Today at 17:00, I will be the proud owner of not one, but two internet connections. I’ve been a Broadstripe customer for the last few years, and the service has been absolutely terrible. Sadly, because cable companies refuse to compete with each other, Broadstripe was my only option for DOCSIS broadband. When we moved in to our house, we had Qwest DSL (now CenturyLink), but it was also terrible: at the time, we were paying for 7mbps, their highest speed, and getting maybe 3mbps on a good day despite several service calls.

MSVC and Templates
Take a look at this snippet of code. Does it look valid to you? On first glance, it might. But if you run it through your compiler… hmm, wait.. MSVC thinks this is valid code too. template <typename A> class Foo { public: Foo() { Bar<A> b; b.method(); } }; template <typename A> class Bar { public: void method() {} }; int main( int argc, char** argv ) { Foo<char> f; return 0; } I’m sure we all know how MSVC is lax when it comes to using typename.
Fixing Git "out of memory" errors on Windows
Googling around, I found a lot of people had the same problem with Git on Windows that I did: large files (where “large” means above 350MB or so) cause “out of memory” errors. A quick look into the file causing the error, Git.pm (ugh, perl), shows the reason right away: they’re doing nice, small 1KB reads of the file blob in a loop… but collecting the whole thing in memory before writing it all out.
SSL: Google vs. F5
Adam Langley, an engineer on Google’s Chrome team, wrote a blog post last summer titled Overclocking SSL. Adam argues that on today’s hardware, SSL connections are not computationally expensive, and showed us some statistics from GMail’s switch to HTTPS by default. He doesn’t go so far as to outright encourage other sites to do the same for their users, but the message is strongly implied. Last week, Lori MacVittie of F5 wrote a blog post (which was at least partially a response to Adam’s post) entitled Dispelling the New SSL Myth, in which she argues that SSL is only inexpensive if you use 1024-bit certificates and easier-to-crack ciphers like RC4.

GameCube power!
Pro tip: If you’re looking for more power for your electronics project than a typical wall wart gives you, your old GameCube power supply will give you 12V at a whopping 3.25A from a fairly small package. The voltage seems pretty steady at 12.19V, so you might even get away without building a regulator circuit. And all this without mangling the power supply’s wires!
A look at modern DVCSs
I’ve been a user of the Bazaar distributed VCS from Canonical (the company behind Ubuntu Linux) for a while now, at least for my personal projects. When I first chose it, I had already spent some time playing with Darcs for a few small projects. Darcs got its start in 2001 with roots in the GNU Arch project. (Bazaar’s predecessor - also named Bazaar - also has its roots in Arch.
Manifest gotchas
For those of you using Visual Studio 2008, and using it’s C++ TR1 support in SP1, here’s something I wish I hadn’t spent so much time tracking down.. TR1 features only exist in 2008 SP1, but the linker will happily build a manifest to link against the pre-SP1 CRT even if you’re using TR1. Some systems (including your development machines) will have proper side-by-side library redirection from the old CRT to the new one.

Multi-button Input Devices
Keyboards are important to me. I used to love pretty, low-profile scissor-key style keyboards. After trying a ergonomic keyboard a few years ago and having it relieve my occasional wrist pain, I never went back. Typing on a non-split keyboard even feels strange now. For about two years I’ve been using the Microsoft Natural Ergonomic 4000 Keyboard both at home and at work. There are a bunch of reasons that this is my favorite keyboard lately: the keys have a very solid action (not as much as the wonderful old IBM Model M, sadly), the enter key is on a single line (as opposed to keyboards with backwards-L shaped enter keys, which push the \ key to be moved elsewhere, often making for a smaller backspace key) and the angle and split of the keyboard has really helped my wrists.
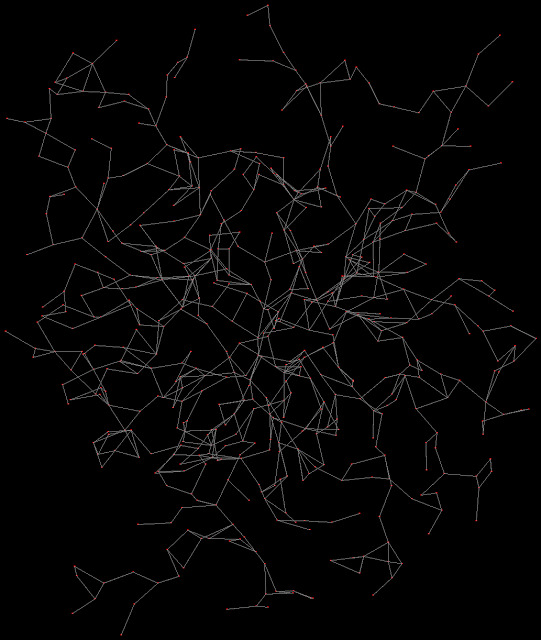
Random Map Creation
This weekend’s project was a better random map generator. Last time, I just generated random points, and then for each system, went through a list of it’s “neighboring” star systems, giving it a random chance to be connected to each system. That random chance declined, the more systems the first system became connected to. In the new version, I’m using an algorithm much closer to one used to generate random mazes.
